-
-
Lock picking
Lock picking fundamentals
Lock picking has been around for centuries and has fascinated people for just as long. It is the art of opening a lock without the use of a key. Lock picking has been used by locksmiths to gain entry to a property when a key has been lost or stolen.... [Read More] -
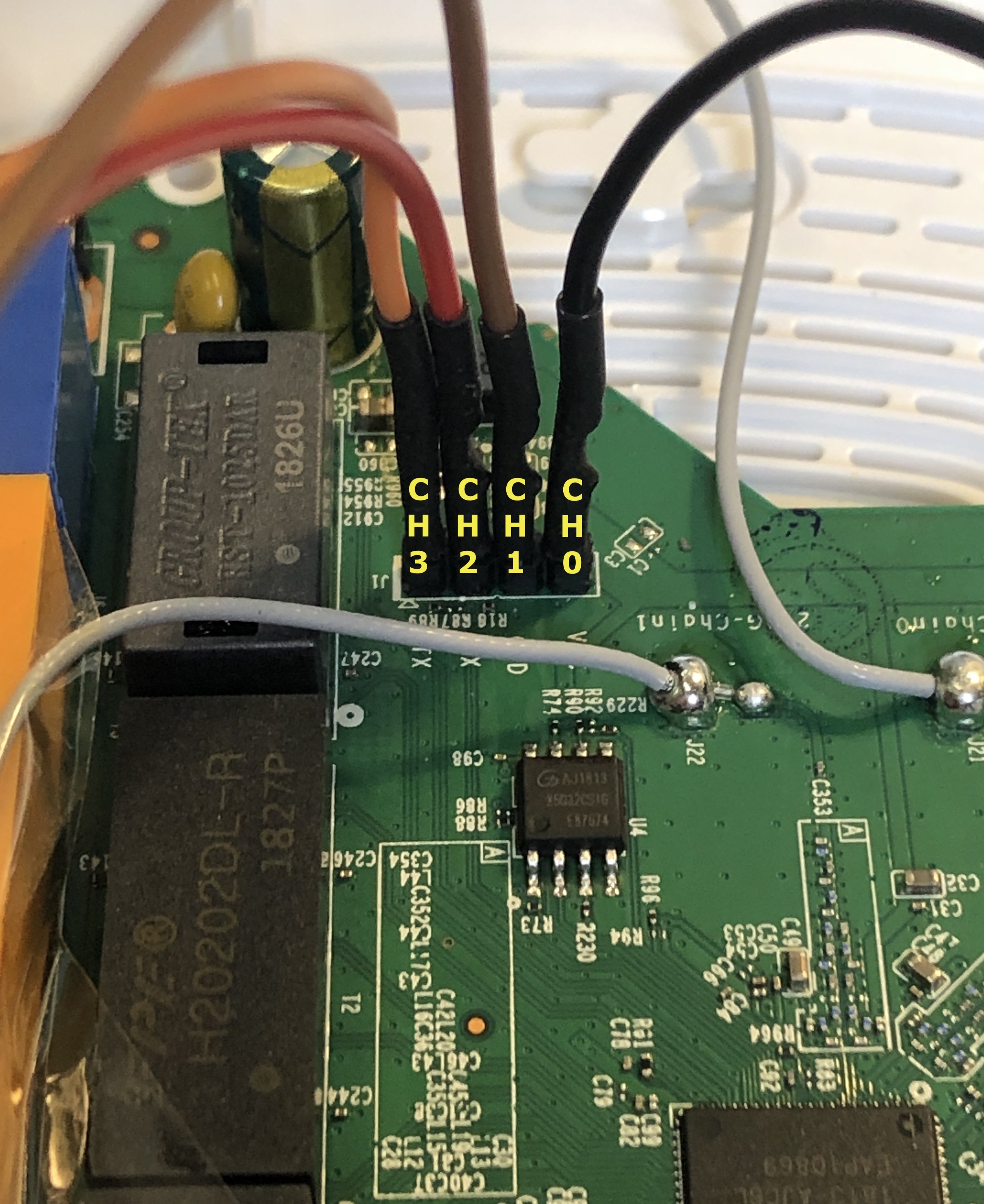
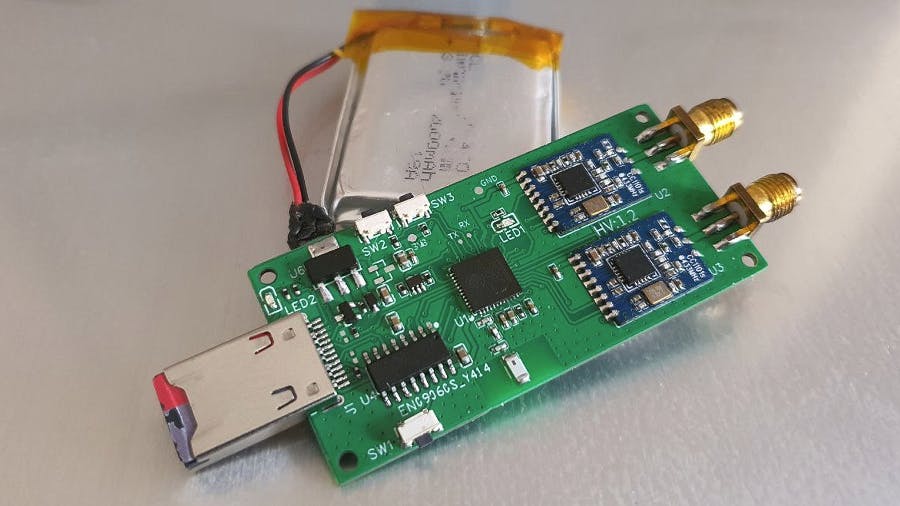
Using EvilCrow RF v2, BusPirate, and Ubertooth for Penetration Testing
A Comprehensive Guide to Analyzing and Exploiting Wireless Networks with Advanced Tools
Wireless networks have become an integral part of our daily lives, and with the rise of the Internet of Things (IoT), the number of wireless devices connected to these networks is only increasing. However, this also means that these networks are more vulnerable to attacks, making it crucial to have... [Read More] -
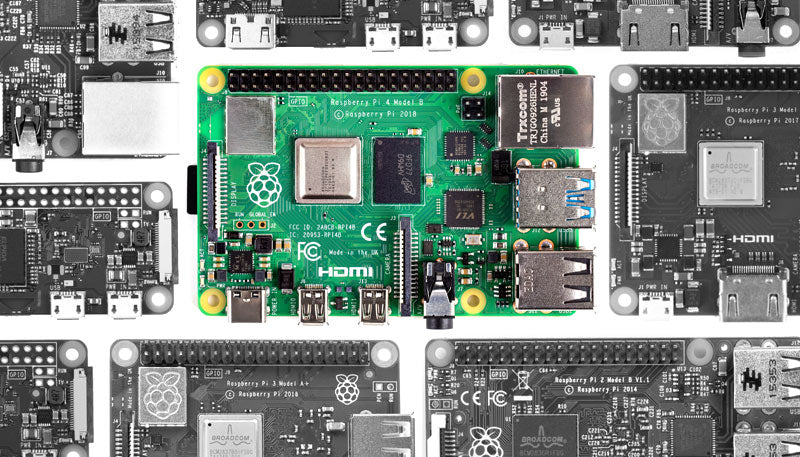
Raspberry pi as a hacking tool
how to use raspberry pi to perform penetration testing
Raspberry Pi is a small, versatile computer that can be used for a wide range of applications. One of the most interesting uses of a Raspberry Pi is for hacking and penetration testing. In this post, we will discuss how to use Raspberry Pi for hacking, including using it as... [Read More]